How do we think about bitcoin staking? [en/cn]
- Published on
This article was co-written with Jane, and the Chinese version is available here.
Restaking is undoubtedly one of the most important topics in the crypto space today. After Ethereum's consensus mechanism transitioned from PoW to PoS, it not only addressed the inflation issue of ETH and endowed them with native staking capabilities, but also opened the possibility of restaking through liquidity staking protocols like Lido, Rocket Pool, and Frax Finance.
Restaking involves depositing LSTs as collaterals to other Actively Validated Services (AVS) and earn corresponding yield, akin to a security rental service. However, in the context of Bitcoin, the term is often used ambiguously, typically referring to using Bitcoin as the staking asset. For clarity and simplicity, the term BTC Staking will be used to denote the use of Bitcoin as the staking asset throughout this article. The concept of "actually BTC Restaking" —— restaking already staked Bitcoin —— remains theoretical without practical examples or use cases, but its feasibility is worth exploring.
The Origins of BTC Staking
Both PoW and PoS are consensus protocols aimed at maintaining synchronization among distributed nodes. The node selection method resembles a lottery, where the weight is represented by a scarce resource —— computational power (hash rate) and energy in PoW, and financial capital in PoS.
There have historically been many debates regarding the superiority of PoW versus PoS. PoW ensures availability under extreme conditions at the cost of probabilistic finality, while PoS offers economic finality but lacks guaranteed availability. The choice between them often revolves around their respective trade-offs rather than the more marketable concerns of energy consumption and environmental impact.
In the long run, Bitcoin might need to evolve towards a more sustainable model like PoS due to diminishing miner incentives caused by token halving. However, in the short term, PoW and PoS are not mutually exclusive systems. For instance, BTC can be used as a staking asset within the PoW ecosystem to introduce staking concepts from PoS chains. From the perspective of Bitcoin holders, BTC Staking creates new use case. From the perspective of borrowing security on PoS chains, BTC can serve as a supplementary or alternative staking asset when native assets are scarce or costly.
But why BTC could be a good staking asset?
- High Market Cap: The high MC is a prerequisite for renting, and security-as-a-service requires liquidity, both of which are readily provided by Bitcoin, the single largest cryptocurrency by market value.
- High Idle Rate: Since Bitcoin mainnet currently lacks support for smart contract, most BTC holders simply hold the asset, anticipating the price appreciation (vs fiat). This high idle rate, combined with its market cap, creates a favorable supply scenario for security renting services.
- Low Volatility and Cost: Most new PoS chains attempt to secure sufficient staking capital by incentivizing users through inflationary rewards of native tokens. However, due to the high volatility of new tokens, a higher APY must be offered to achieve the same risk-adjusted return and attract users to hold and stake. Additionally, new PoS networks face a potential death spiral: when token prices drop, the TVL in the network decreases, leading to reduced security, which can further drive down token prices. In contrast, Bitcoin, with its long history and low volatility, benefits from the Lindy Effect and can provide security to PoS chains at a lower cost.
Considering the above points, most people can understand that BTC would be a high-quality staking asset. However, the challenge lies in its implementation.
Implementing BTC Staking
Currently, there are two mainstream methods for implementing BTC Staking:
- Bridging: This intuitive and relatively simple method involves bridging Bitcoin to a PoS chain that supports smart contracts, using this "bridged version of Bitcoin" as the staking asset.
- Remote Staking: This method keeps Bitcoin on the Bitcoin mainnet and allows staking on other PoS chains remotely. The core challenge here is ensuring that the PoS chain can immediately, permissionlessly, and trustlessly slash the staked Bitcoin on the mainnet in case of misbehavior.
Bridging to PoS Chains — BounceBit
Most current Bitcoin Layer 2 solutions transfer native Bitcoin to other PoS chains through bridges or mirroring. For instance, Stacks uses the Proof of Transfer (PoX) mechanism to convert Bitcoin into sBTC; CoreDAO employs a multi-signature bridge to create coreBTC; B² Network uses a bridge to issue B² BTC; and BounceBit uses a bridge to convert Bitcoin into BBTC.
These methods are similar, differing only in the degree of trustlessness of the bridge: some use fewer multi-signatures, some use more multi-signatures, some use random multi-signatures, and some use mirroring. However, all these methods introduce new trust assumptions.

Taking BounceBit as an example, as shown in the architectural diagram above, users can deposit Bitcoin into the BounceBit Protocol, which then keeps the assets in a MPC custodial account. The BounceBit Chain, an EVM-compatible chain, then issues users with BBTC (BounceBit BTC) at a 1:1 ratio as a deposit certificate. Subsequently, familiar activities such as staking, re-staking, and using DeFi scenarios follow. This approach doesn't directly tackle technical challenges but leverages the public trust in MPC custodial accounts, offering an efficient and practical strategy. For more details on its operation, please refer to a previous article (in chinese) we wrote.
Remote Staking — Babylon
Simple mirroring and bridging are not ideal for staking. Mirroring lacks the PoS chain's ability to penalize BTC on the Bitcoin mainnet, which hardly qualifies as a PoS mechanism; bridges, due to the absence of a native smart contract layer on the Bitcoin mainnet, are challenging to construct securely in any meaningful sense and require additional trust in third parties.
For Bitcoin holders, ensuring the security of their Bitcoin assets is the first priority, followed by the potential returns. When Bitcoin bridges cannot sufficiently trustless, keeping assets on the Bitcoin mainnet is a prerequisite.
For PoS chains seeking security, the core issue is how to implement an immediate, trustless slash mechanism for assets on the Bitcoin mainnet. With Turing-complete smart contract layers on both sides, implementing a slash mechanism is easy. For instance, Eigenlayer's Modular Dual Staking between Ethereum and AVS, or Mesh Security between Cosmos Hub and Cosmos Zone, are feasible.
Given the current limitations of Bitcoin, Babylon proposes what seems to be the best technical solution from a credible neutrality standpoint.
How does Babylon operate?
The staking mechanism is crucially dependent on a trustless and effective slash mechanism. To achieve BTC Staking, we can break it down into the following smaller objectives:
- Staking must occur while Bitcoin remains on the Bitcoin mainnet.
- There must be a mechanism to judge whether nodes are acting maliciously.
- In the absence of malicious behavior, stakers should be able to retrieve their staking assets and rewards without permission after the unbonding period.
- In cases of malicious behavior, the PoS chain must be able to penalize the BTC on the Bitcoin mainnet within the unbonding period, without permission.
For remote staking with BTC remaining on the Bitcoin mainnet, essential conditions include the ability for immediate, bidirectional communication between the Bitcoin mainnet and the PoS chain. Babylon's approach involves a three-layer structure, with the Babylon Chain acting as a communication layer, as it is challenging to directly transmit substantial information from PoS chains to the Bitcoin mainnet without processing and compression.
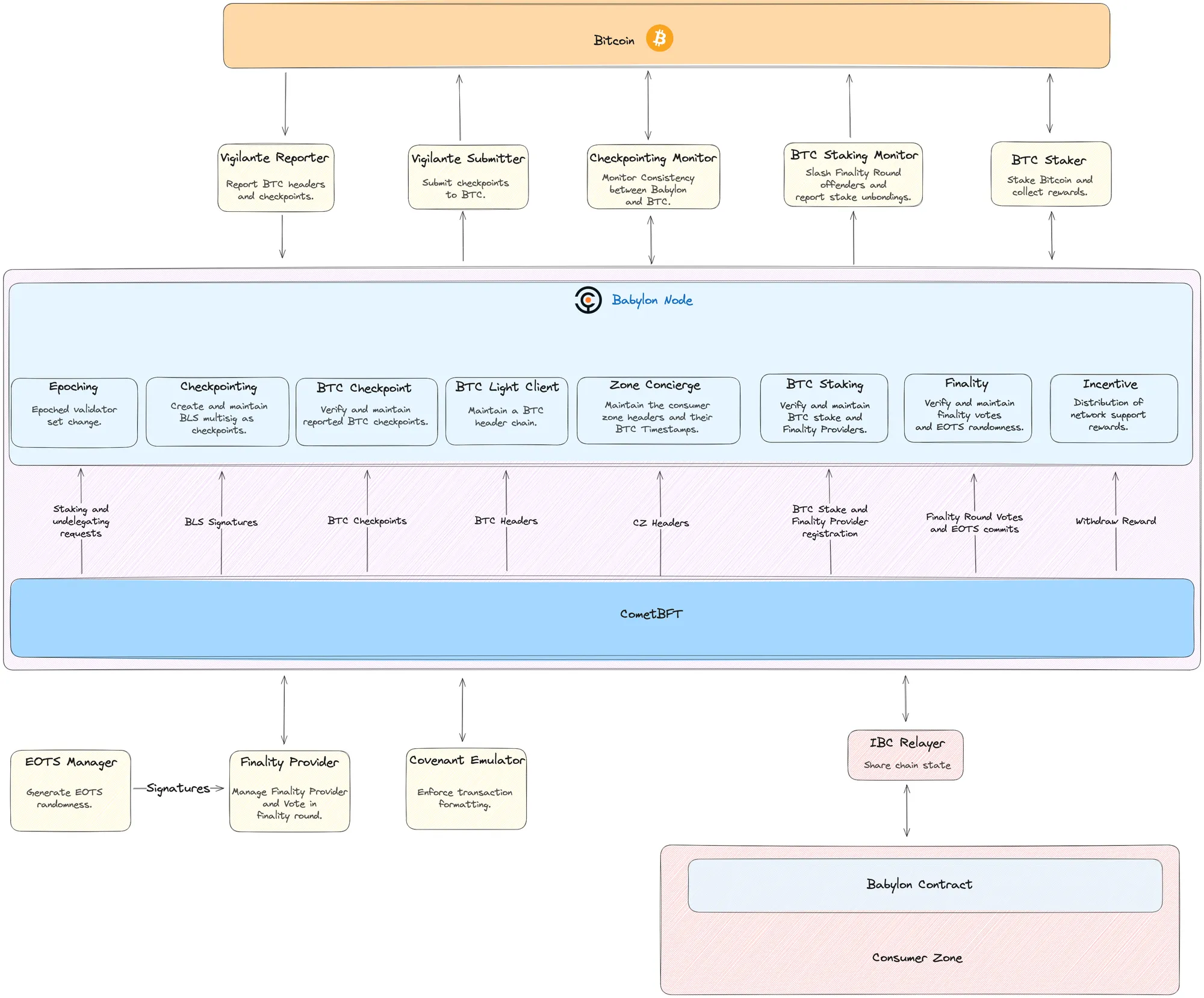
Specifically, Babylon Chain maintains two-way communication with two blockchains (PoS chain and Bitcoin mainnet). On the PoS chain side, it uses the IBC Relayer for communication; on the Bitcoin mainnet side, it uses the Vigilante Reporter to transmit messages from the Bitcoin mainnet to Babylon Chain, and the Vigilante Submitter to relay messages from Babylon Chain to the Bitcoin mainnet. It also employs the Checkpointing Monitor to supervise the accuracy of two-way communications, the BTC Staker to log staking-related information, and the BTC Staking Monitor to handle issues related to slash.
There are two mainstream slash mechanism to determine the misconducts:
- In the Ethereum-used Casper consensus mechanism, there are two slash conditions: a1) signing two different blocks at the same block height, a2) nodes must not vote within the span of its other votes. For more details, please refer to this article.

- In the Cosmos-used CometBFT consensus engine, there are also two slash conditions: b1) signing two different blocks at the same block height, b2) nodes conducting an Amnesia Attack.
For a1 and b1, Babylon has introduced EOTS (Extractable One-Time Signatures) as a solution. Nodes on Babylon Chain use EOTS for signing, which exposes the private key automatically when used to sign two transactions with the same private key. In other words, anyone can deduce the signer's private key from the information in both transactions, effectively solving the problem of signing two different blocks at the same height.
For a2 and b2, as there is no good equivalent solution, Babylon adds an "additional EOTS-based voting round" on top of the original CometBFT mechanism, known as the "Finality Round." This is understood as having nodes cast an initial vote to achieve a basic consensus, followed by another group of nodes (Finality Providers) casting an additional vote to reaffirm this consensus. The condition for achieving consensus the second round is obtaining signatures from over two-thirds of the staking weight using EOTS. Consensus is only considered successfully achieved if it is reached in both rounds. The modular nature of this solution has a significant advantage, allowing compatibility with other commonly used Finality Gadget consensus systems in PoS.

In cases where there is no malfeasance, staking users wishing to retrieve their assets can do so by adding a time lock on the UTXO, with the timespan of this timelock also known as the unbonding period. In cases of malfeasance, penalties are directly enforced through the aforementioned EOTS method. This describes Babylon Chain's approach to consensus achievement, malfeasance judgment, and slash enforcement. Notably, EOTS is enabled by Schnorr signatures, a feature introduced with the Taproot upgrade on the Bitcoin mainnet.
Timestamps, Unbonding Times, and Long-Range Attacks
Unlike PoW, PoS does not employ Nakamoto Consensus, which leads to the possibility of long-range attack. This possibility often results in a longer unbonding period for PoS chain.
A long-range attack occurs when attackers, possessing the private keys (or voting power) of a majority of nodes from a past block, exploit the reusable nature of voting power to rapidly produce a large volume of "fake blocks" in their controlled 'small world' — potentially even outpacing the block history of the external real world. In replicating legitimate timestamps, new nodes are unable to distinguish between a chain that took significant real-world time to develop and one rapidly fabricated by an attacker. This issue arises because, in the blockchain world, time progresses through the creation of new blocks and lacks an external time reference.
Previously, this was addressed through social consensus, such as regularly publishing legitimate hash of block on websites or forums of blockchain's foundation, which helps new nodes in choosing between two different chain histories. This is referred to as "weak subjectivity" by Vitalik.
However, in the case of Babylon, if the previously mentioned timestamping technique that allows communication between two chains is utilized, it effectively introduces external time from the Bitcoin mainnet into the PoS chain, addressing long-range attacks and allowing for a shorter unbonding period, such as six Bitcoin blocks (approximately one hour).
Balancing Renting Security Renting with Native Security (PoS Chain Perspective)
BTC staking does not mean completely replacing native token staking. In fact, PoS chain can secure their networks using a combination of assets (Bitcoin + native tokens), and more. Considering the different costs of using Bitcoin and native tokens, staking rewards often need specific designs and may include native tokens or revenue sharing.
Regarding security, let's consider "diversity of funds" and TVL.
From the perspective of funds' diversity, introducing external staking assets and nodes, regardless of the method, undoubtedly increases decentralization and network resilience. Possible methods include:
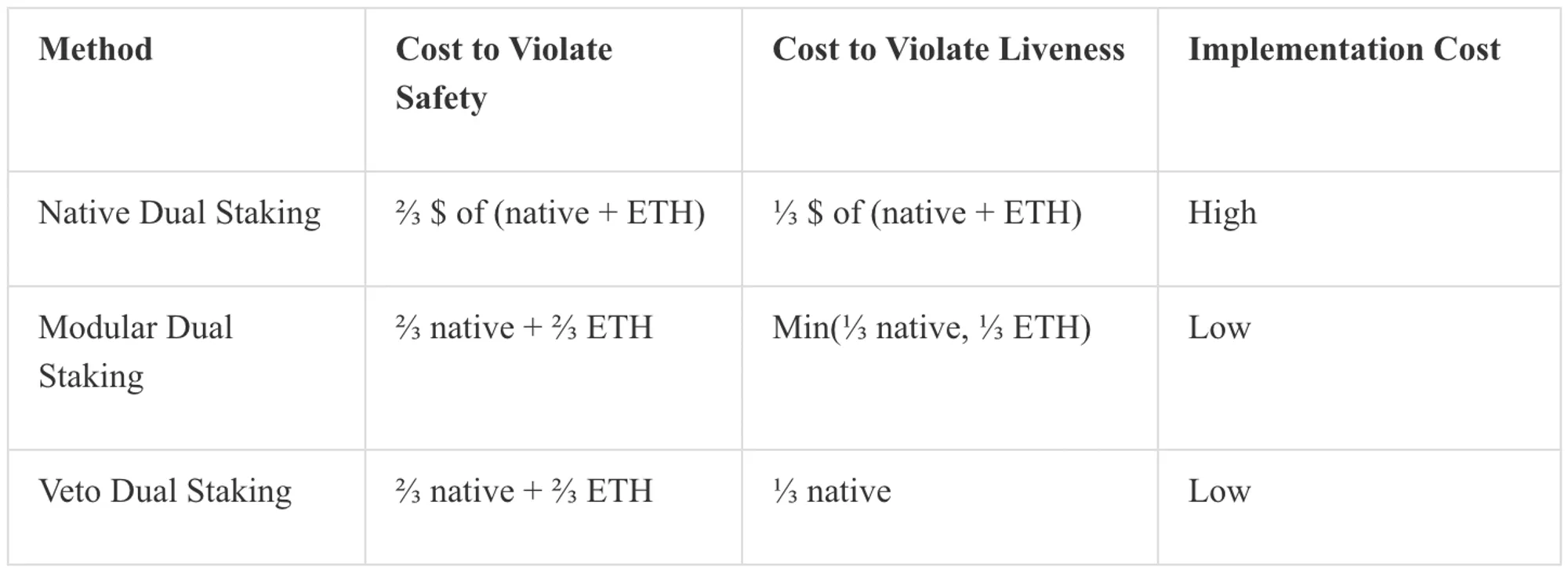
- Native Dual Staking: Native token and ETH are considered as sigle staking asset, with staking weight converted via oracle, and consensus is only required to reach the threshold.
- Modular Dual Staking: Consensus requires support from both native token operators and ETH operators, each meeting a strict standard; thus, an attacker targeting the operator with lower security could prevent achieving the consensus.
- Veto Dual Staking: Native token operators must meet a certain quantitative standard, similar to traditional PoS. ETH operators serve as an additional layer of security, with the right to veto if native token operators err. This model differs in usability from modular dual staking: even if ETH-based operators are offline, the PoS network can still function.
From a TVL perspective, if the TVL bridged to a specific chain is $5M, to have the slashable assets equal to the TVL, a safety threshold of 1.5 times (corresponding to a 2/3 threshold for slash) is advisable, implying that the staking assets should ideally be no less than $7.5M. If the current native token assets pledged are only $5.5M, this indicates a safety budget shortfall of at least $2M. In such cases, one could prioritize introducing tokens from closely related protocols as auxiliary staking assets. If deficits persist, external security measures such as BTC or ETH may be considered. In essence, services like Babylon function like mercenaries, providing security as a paid service when necessary.
Besides the differing holding costs, native token holders, after receiving staking rewards, are more likely to retain their tokens, while LSTs stakers may quickly sell off their rewards for profit, potentially leading to selling pressure on the native tokens. From this perspective, projects may consider using the security provided by services like Babylon as a supplement and evaluate the safety costs under different scenarios. This also implies that fully outsourcing security is risky, and maintaining an independent set of validators is a better option.
From the perspective of security renting, despite the lower costs of borrowing Bitcoin or Ethereum, the loyalty of these capital is not within one’s own ecosystem, necessitating a consideration of potential selling pressures. Different projects may prioritize the TVL and diversity of capital differently. Experience shows that borrowing from a few concentrated providers generally costs less per unit but comes at the expense of centralization; however, the key here is that different projects have the right to choose.
Choosing Quality Security Lenders (Node Operator's Perspective)
In a well-developed, decentralized security renting market, security providers should be free to commit to any specific AVS. However, if the AVS ecosystem thrives as expected, how should one correctly choose and allocate among hundreds of AVS? We believe the definition of 'excellent' should balance returns and security.
Whether solo staking or handing over tokens to a staking provider, the rationale remains similar to that of traditional node operators (NOs). We can draw directly from their experience for guidance. Common selection criteria include ensuring the lender has a good development team, publicly auditable code, sustainable returns, a rewarding ratio for security providers, team experience, fundraising status, and investor reputation.
Another core aspect is that the return of AVSs will likely exhibit a power-law distribution, with returns concentrated at the top. Thus, early involvement in high-quality AVSs can be a source of alpha. Conversely, engaging all long-tail AVSs is not the good idea as it introduces complexity and risk, possibly requiring NOs to charge high commissions to mitigate the risk-adjusted returns for stakers. This also introduces increased slash risks.
Further consideration is given to the potential of an AVS; if widely recognized as promising, it could secure security with relatively fewer token rewards due to expected token value appreciation. Given the volatility of token prices, NOs also need to select some AVSs that provide income-based rewards, ensuring a minimum income guarantee.
Future Evolution of the Security Renting Market (Marketplace Perspective)
The worlds of blockchain enable selfish individuals to reach consensus in a trustless manner through mechanisms. In the world of PoS, consensus can be understood as staking, and the slashable nature of staking as a source of security, thus “security renting" can be viewed as an abstraction of the core problem in blockchain.
Services like Babylon aim to create a security marketplace, essentially aiming to establish an efficient bilateral market for security supply and demand. The current challenge lies in the lack of a comprehensive and diverse renting ecosystem with profitable AVSs being scarce. The solution? Demand side dictates the short-term view while supply side shapes the long term.
From the demand side:
Regarding "whether there is demand," setting aside the magnitude, it’s understood that demand genuinely exists. If the value and market positioning of AppChains can be more broadly understood, or if new types of AVSs can be designed, the market for security renting can become more robust and prosperous.
On whether "demanders can provide sustainable real yields," we believe this is somewhat affirmative. For instance, DA layers can earn through storage fees, Oracles through fetch-data fees, and PoS through sharing MEV income and transaction fees, all of which are real and sustainable revenues.
From the supply side, Babylon needs to convince the Bitcoin community that it can ensure asset security, while Eigenlayer needs to assure the Ethereum community that they are not overusing Ethereum's consensus. Regarding the stability of capital, considering higher rewards for those willing to stake long-term could be an option. Additionally, establishing a quality supply side starts with making the concept of "security as a service" practical, then easy to use, and finally scalable. For instance, Sreeram Kannan's narrative about building Eigenlayer into a cloud service for cryptocurrencies is an example. Through economies of scale, security providers can effectively decrease the cost of security and allow users to scale immediately with business growth. AVSs built on Eigenlayer could follow a modular service route, providing a SaaS-like experience to other projects and ecosystems, thereby establishing a robust and resilient ecosystem around Eigenlayer and AVS.
Various Methods of Participate the Restaking Trend
As a pivotal narrative and foundational element in the industry for this year and the foreseeable future, different projects must consider how to integrate the element of restaking. Broadly, this can be categorized into two main approaches:
1. Integrating Restaking-related Assets:
For DeFi protocol, it is straightforward to consider how to incorporate LSTs into their ecosystem. Potential directions include using LSTs as collateral in lending protocol and providing liquidity in DEX protocol.
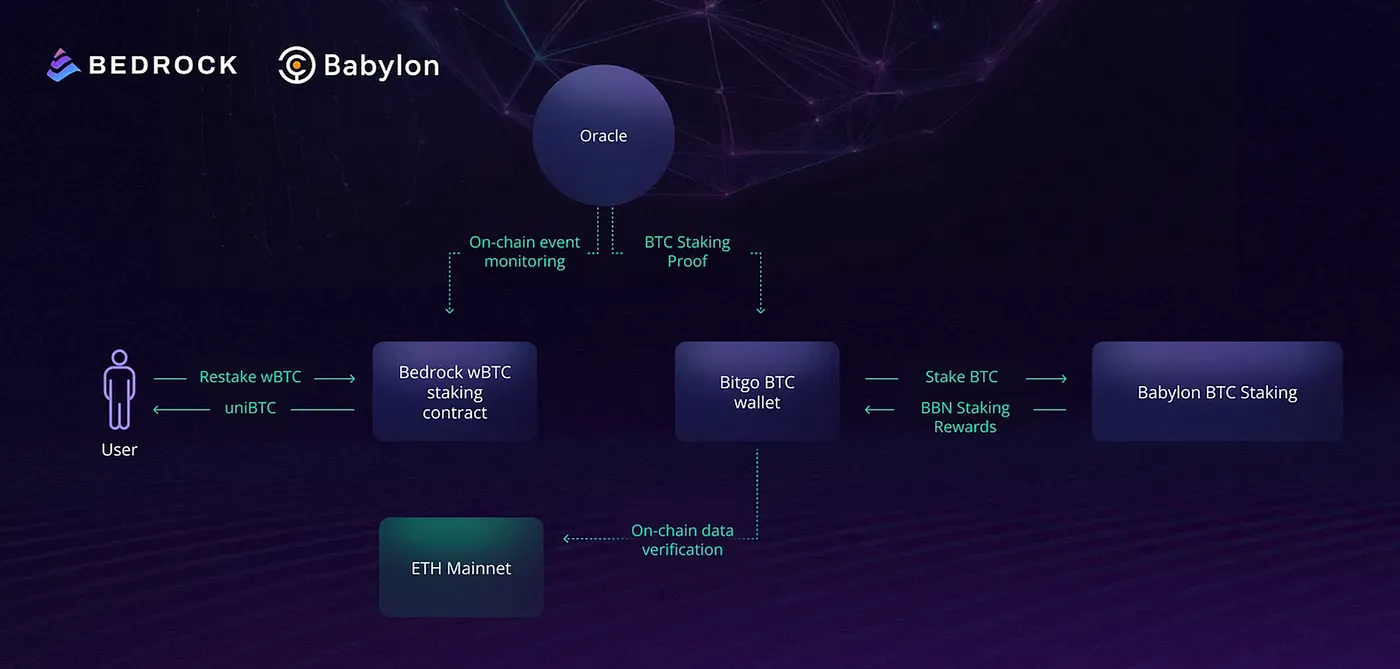
For instance, Bedrock, a liquidity restaking protocol, recently introduced uniBTC for wBTC holders on Ethereum, offering a restaking solution. This offers deeper liquidity compared to direct staking on Babylon, and apart from earning rewards from Babylon, holders can also gain Bedrock's diamond point rewards.

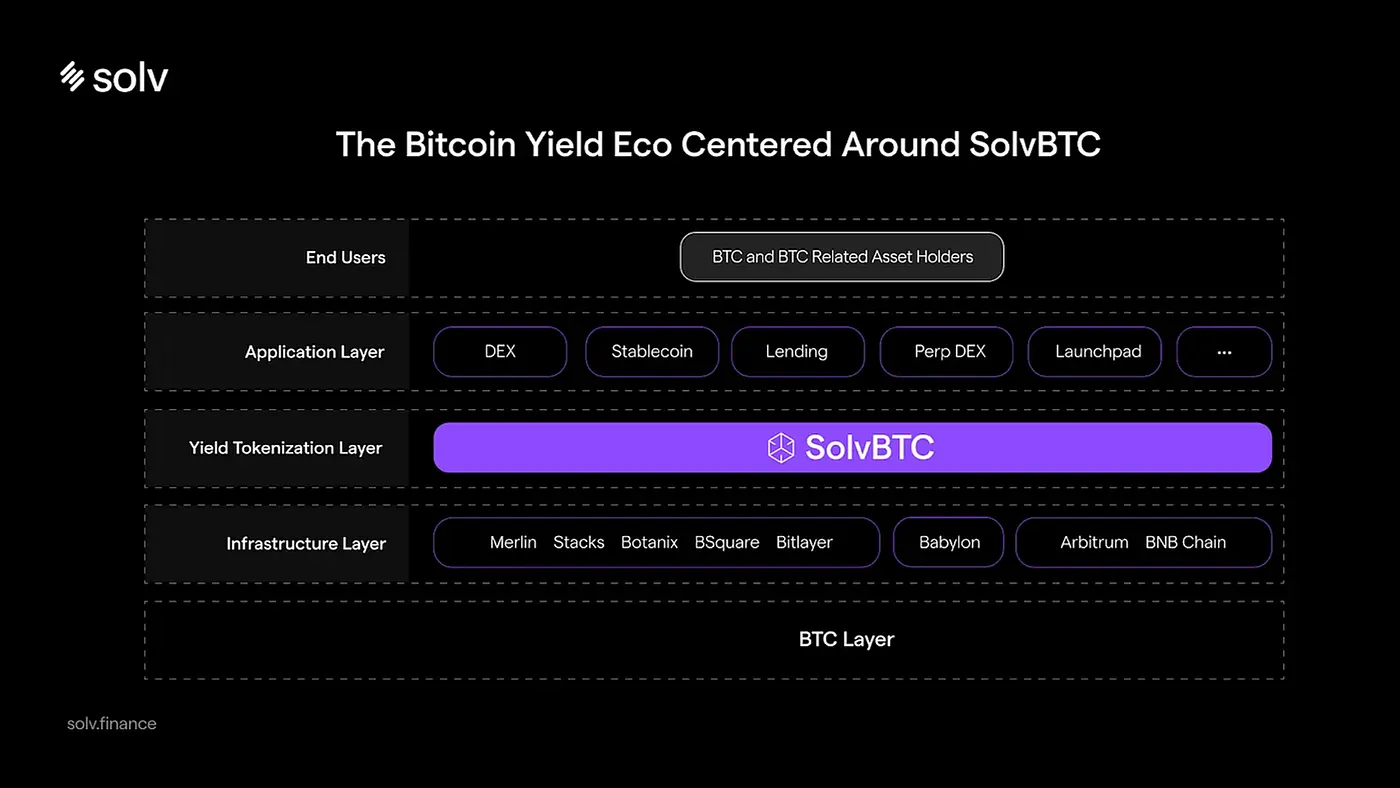
Moreover, platforms like Solv Protocol have integrated Babylon’s restaking yields into their delta-neutral earnings strategies.

2. Renting Security as Infrastructure:
Renting security is a more universal application scenario. infrastructures with high decentralization requirements and limited initial staking capital might consider this option. Potential directions include services related to rollups (sequencers, bridges, MEV-related services, etc.), co-processors (verifiable databases, AI interfaces, e.g. Ritual), cryptographic applications (TEE Network, secret sharing, FHE, examples include Inco, Fhenix), and proof applications (identity, address proofing, etc.). This has opened new on-chain scenarios, particularly in co-processors and cryptographic applications, which are just begin to emerge.
For example, Cyber recently announced its shift to Layer 2, utilizing Eigenlayer's AVS to build a decentralized Infra including sequencers, validators, and CyberDB. Although partnering with Eigenlayer rather than Babylon, the idea of renting security is the same. Cyber employs a dual staking model where users can stake Cyber or LRTs (currently supporting ezETH, pufETH, weETH) to earn multiple sources of return, including ETH staking rewards, restaking yields from Eigenlayer, and points from LRT and Cyber, ensuring security with both Cyber and LRT tokens.

The dual staking model has a key advantage: it supports network cold starts by renting ETH, mitigating the impact of potential death spirals. For example, when the native token's price falls, although the security of the PoS network might be compromised, the consequences are relatively controlled thanks to the economic security provided by LRTs.
Conclusion
Security is the core of blockchain, and opening the security of the two largest cryptocurrencies to other applications and developers will undoubtedly have a lasting and profound impact.
Regarding the sharing of security between PoW and PoS worlds, using first principles, it can be categorized into four types.
- PoW to PoW: like Merged Mining by Rootstock
- PoS to PoS: such as "Eigenlayer's restaking" and "Hub and Zone on Cosmos ecosystem"
- PoW to PoS: like Babylon using PoW assets for PoS staking
- PoS to PoW: which is less explored but could involve converting RWA assets to support PoW with tokenized computing power.
In a broader sense, the key to security renting lies in how the underlying consensus is achieved, how this consensus is protocolized, productized, scaled, and how it fosters a thriving cloud service ecosystem. The efficient collaboration and better resource and data sharing between various AVSs are not only in line with the original Cypherpunk spirit but also the source of true value.
The possibilities are vast and still unfolding, such as fair distribution models for AVS yields, the emergence of new AVS types, and the combination of various services like LEGO. The exploration of Restaking is just beginning, and it's worth continuously monitoring its evolution, iteration, and the accompanying opportunities.
Reference
跳進名為Babylon的兔子洞,我們誤闖了安全性租賃的國度
本文與 Jane 共同研究撰寫
再質押(Restaking)無疑是當下 Web3 領域中最重要的話題之一。以太坊的共識機制從工作量證明(Proof-of-Work, PoW)平穩的過渡到權益證明(Proof-of-Stake, PoS)之後,除了解決 ETH 代幣長期通脹的問題、為其賦予了(全新的)原生質押功能外,也通過如 Lido、Rocket Pool、Frax Finance 等流動性質押(Liquidity Staking)的協議,開啟了再質押的可能性。
再質押的本質是使用 LST 這類型的流動性資產,向其他 AVS 提供安全保障,以獲取相對應的收益,可視為是安全性的租借服務。但在比特幣的語境之下,目前對名詞的定義相對混亂,往往講的“再質押”,指的是使用比特幣作為質押資產(BTC as the staking asset)。為了簡潔與清楚起見,下文將這種以「比特幣作為質押資產」的做法,統一稱之為 BTC Staking;在此基礎上,假設能在技術上,將已經質押過的比特幣,再次拿去質押時,才會是所謂的 BTC Restaking(目前尚未有好的案例與使用場景,我們也會論證這件事情存在的合理性)。
BTC Staking 成立的原點
PoW 與 PoS 皆是一種共識協議,其目的是保持分佈式節點(Node)之間的同步。保持同步的方式是選出一個節點,以這個節點為準。選出的方式如同樂透抽獎,權重則是由一種稀缺資源作為代表,在 PoW 的情況下,稀缺資源就是算力(hash rate),以及背後所代表的物理能量;在 PoS 的情況下這個稀缺資源就是資本。
關於兩者的優劣,在歷史上有過無數的爭論。PoW 能夠在極端況下保證可用性(Liveness),但以只能獲取概率上的確定性(Probabilistic Finality)為代價;PoS 反之,它可以獲得經濟上的確定性(Economic Finality),但可用性卻不能獲得保障。兩者之間的選擇,更多的是圍繞在這兩種特徵的取捨,而非容易被拿來作為營銷的環保與能耗。
縱使長期來看,比特幣由於代幣獎勵的不斷減半,有礦工經濟激勵不可持續的隱患,所以可能需要在共識機制層面往 PoS 等相對永續的模型迭代。但短期的實際操作上,PoW 與 PoS 兩者並不是對立的系統,例如可以將比特幣作為質押資產,在 PoW 生態中引入 PoS 的質押概念。從比特幣持有者的角度,BTC Staking 為其創造了一個新的使用場景;從 PoS 鏈租借安全性的角度,比特幣可以作為質押資產(暫時性)不足或是成本高昂時的補充替代方案。
但從 PoS 鏈的角度,為什麼比特幣相對其他加密貨幣是一種好的質押資產呢?
- 高市值:資金的充沛性(abundance)是租借的前提,安全即服務(Security-as-a-Service, SaaS)也是需要流動性的,而比特幣無疑是市值最大的單一加密貨幣(過萬億美金)。
- 高閒置率:由於尚未能原生支援智能合約(Smart Contract),比特幣主網目前欠缺除了支付以外的完整生態。多數的比特幣持有者只是單純的持有,並期待其增值。高閒置率加上高市值,為安全性租賃服務塑造了良好的供給。
- 低波動性導致的低成本:多數新 PoS 鏈想獲得足夠多的資金質押的方式,是通過獎勵原生代幣的通脹手段來吸引用戶質押。不過由於新代幣往往波動性高,需要提供更高的年化報酬(APY),才能達到相同的風險修正後報酬(Risk-Adjusted Return)以吸引用戶來持有並質押。此外,新的 PoS 網路也存在一個潛在的死亡螺旋:當代幣價格下跌時,會使整體網路的 TVL 下降,也代表著安全性的下降,而這容易引起代幣價格進一步的下跌。相對的,比特幣由於歷史悠久,波動性低,在林迪效應(Lindy Effect)的加持下,能以更低的成本為 PoS 鏈提供安全性。
綜合以上三點,多數人都能理解比特幣會是一種優質的質押資產,不過這件事情的難度在於實踐:合理只是擁有地圖與行程,實踐它們才是真的踏上旅程。
兩條路徑的選擇
要實現 BTC Staking,當下有兩種主流的手段:
- 橋接:先將比特幣橋接(Bridge)至能支持智能合約的 PoS 鏈,再使用這種“橋接版本的比特幣”作為質押資產,這是一種直覺且相對簡單的做法。
- 遠程質押:讓比特幣保留在比特幣主網上面,通過遠程的方式在其他 PoS 鏈上進行質押,這種方式的核心在於,當節點作惡時,PoS 鏈要有能力對在比特幣主網上的比特幣進行即時的、無許可的(Permissionless)、去信任的(Trustless)罰沒(Slash),而如何在當前比特幣原有性能上實現罰沒,是一個工程上極有挑戰的事情。
我們以 Bouncebit 與 Babylon 為例來探討具體的解法細節。
橋接至 PoS 鏈——BounceBit
絕大多數當下 Bitcoin L2 的解法,是通過橋或映射(Mirror)的形式,先將原生的比特幣轉移至其他 PoS 鏈上。例如 Stacks 用 Proof of transfer (PoX) 的機制將比特幣包裝成 sBTC;CoreDAO 用多簽橋將比特幣包裝成 coreBTC;B² Network 用橋將比特幣包裝成 B² BTC;BounceBit 用橋將比特幣包裝成 BBTC。
這些方式大同小異,差異在於橋的去信任程度:有些用較少的多簽、有些用更多的多簽、有些用隨機多簽等、有的用映射,但都還是需要引入新的信任假設。

以 BounceBit 為例,參考上面的架構圖,用戶可以通過 BounceBit Protocol 將比特幣存入,接著 BounceBit Protocol 會將用戶存入的資產,保留在一個多方計算(Multi-Party Computation, MPC)的托管帳戶中(並且不會離開),再在 BounceBit Chain 這條 EVM 兼容的鏈上,以 1:1 的形式,給到用戶 BBTC (BounceBit BTC) 作為存款憑證。接著就會是大家所熟悉的質押、再質押、DeFi 等使用場景了。這種不直面技術難點,但借用大眾對 MPC 託管帳戶信任的手段,不失為一種高效務實的策略。其具體運作方式與細節,可以參考這篇之前寫的文章。
遠程質押 — — Babylon
單純映射與橋不會是 staking 最理想的方式。單純映射不具備 PoS 鏈對於在比特幣主網上的比特幣進行懲罰的能力,這似乎連 PoS 機制都稱不上;橋則由於比特幣主網尚未有原生的智能合約層,很難搭建出在各種意義上可以稱之為安全的橋,需要引入額外的對於第三方的信任。
對於比特幣持有者而言,首先是需要先保證比特幣資產的安全,其次才會是考量能獲取的收益。在比特幣橋還無法做到足夠的去信任時,將資產放置在比特幣主網是一個前提。
對於想租用安全性的 PoS 鏈而言,核心在於如何對在比特幣主網上的資產,存在一套即時有效的、去信任的罰沒機制(Slash Mechanism)。在雙邊都具有圖靈完備的智能合約層的條件下,存在一套罰沒機制並不困難。例如在以太坊與 AVS 之間能通過 Eigenlayer 的 Modular Dual Staking,或是 Cosmos Hub 與 Cosmos Zone 之間能通過 Mesh Security。
在當前比特幣的限制條件下,從可信的中立性(Credible Neutrality)考量,Babylon 提出了似乎是當下最好的技術層面的解決方案。
Babylon 是如何運作的?
質押機制的成立,關鍵在於存在一套去信任且有效的罰沒機制。想要實現 BTC Staking,我們可以拆分成以下幾個小目標:
- 比特幣需要停留在比特幣主網的情況下進行質押。
- 需要有一套判斷節點有無作惡的機制。
- 在沒有作惡的情況下,質押者可以在解綁期(Unbonding Period)之後,無許可的取回自己的資產與質押獎勵。
- 在作惡的情況下,PoS 鏈要能在解綁期之內,無許可的對於在比特幣主網上的比特幣進行罰沒。
為了讓比特幣能停留在比特幣主網的情況下進行遠程質押,必要條件是比特幣主網與 PoS 鏈之間能進行雙向即時溝通。Babylon 的作法是設計了一個三層的結構,讓 Babylon Chain 充當了兩者溝通的橋樑,畢竟很難想像不經過壓縮與處理,直接的把大量 PoS 鏈上的資訊傳遞到比特幣主網。
具體來說,Babylon Chain 會雙向地與兩條鏈保持溝通,在 PoS 鏈那端,它們使用 IBC Relayer 來溝通;在比特幣主網那端,它們使用 Vigilante Reporter 讓訊息從比特幣主網傳遞到 Babylon Chain,用 Vigilante Submitter 讓訊息從 Babylon Chain 傳遞到比特幣主網,用 Checkpointing Monitor 監督雙向的訊息正確,用 BTC Staker 紀錄質押相關的資訊,用 BTC Staking Monitor 處理罰沒相關的問題。
PoS 機制關於作惡的判斷有兩種主流的作法:
- 在以太坊使用的 Casper 共識機制中,罰沒情況有兩種:a1)在同個區塊高度,給兩個不同的區塊簽署,a2)節點不可投出高度圍繞於另一投票高度的投票,更詳細的資訊可以參考這篇文章。

- 在 Cosmos 使用的 CometBFT 共識引擎中,罰沒情況也有兩種:b1)在同個區塊高度,給兩個不同的區塊簽署,b2)節點進行了健忘攻擊(Amnesia Attack)。
關於 a1 與 b1,Babylon 引入了 EOTS(Extractable One-Time Signatures)來解決。Babylon Chain 上的節點使用 EOTS 來簽章(也就是投票),它的特性是,當用同一個私鑰,去簽兩筆交易的時候,私鑰會自動地暴露出來。換句話說,也就是任何人都能拿那兩筆交易的資訊,回推出簽署者的私鑰。這能等價地解決“在同個區塊高度,給兩個不同的區塊簽署”的問題。(accountable assertions)
關於 a2 與 b2,由於沒有好的等價解法,所以 Babylon 在原先的 CometBFT 共識機制基礎上,引入“額外的使用 EOTS 的共識輪”來解決,也就是所謂的“Finality Round”,可以理解為,節點先投一次票,達成基本的共識基礎後,再找另一群節點(Finality Provider)來額外投一次票,再次確認這個共識,第二次達成共識的條件是獲得超過三分之二質押權益的 EOTS 簽名。而只有兩次都存在共識時,才被判斷為成功達成共識。這種解法明顯的好處在於其模塊化特性,能兼容其他 PoS 常用的 Finality Gadget 共識系統。

在沒有作惡的情況,質押用戶想取回自己資產,可以通過在 UTXO 的花費條件上加上一個時間鎖(也就是所謂的解鎖期)來解決。在作惡的情況,會通過上述的 EOTS 的方式直接進行罰沒。至此,這是 Babylon Chain 達成共識、判斷作惡、進行罰沒的方式。另外值得一提的是,EOTS 是通過 Schnorr 簽章實現的,這也是在比特幣主網進行了 Taproot 升級之後新引入的功能。
時間戳、解綁時間和長程攻擊
相對於 PoW,由於 PoS 不存在中本聰共識(Nakamoto Consensus),也就導致存在長程攻擊(Long-Range Attack)的可能性,也因為這個可能性,往往 PoS 會有一個相對更久的解鎖期。
長程攻擊指的是,當有攻擊者,掌握了歷史上某一任意區塊的大多數節點的私鑰(也就是投票權重)時,可以通過投票權重可以重複使用的特性,在自己的已控制節點的小世界中,快速產生大量自行捏造的區塊(甚至可以比外界的區塊歷史還長)。在複製合法的時間戳的情況下,能讓新加入的節點無法分辨,哪一個是花了許多現實時間產生的鏈,哪一個是攻擊者在短時間內捏造的鏈。這其中的根本原因,是由於區塊鏈是通過增添新的區塊來代表其原生時間的前進,不存在一個外生的時間。
之前的解法是通過社群共識(Social Consensus)來解決,例如定期在某個地方,例如基金會的網站、論壇等,告訴大家真實合法的區塊長什麼樣子(Checkpoint),讓之後進來的節點,看到兩個不同鏈的歷史數據時,就能選擇。這被 Vitalik 稱之為弱主觀性(Weak Subjectivity)。
但在 Babylon 的情況下,如果用上前面提到的讓兩條鏈能相互溝通的 timestampping 的手法,則可以變相的在 PoS 鏈上,引入了比特幣主網的外生時間,也就是能直接解決長程攻擊,同時也讓質押的解鎖期可以縮短到,例如六個比特幣區塊(約一個小時)。
外部安全性租賃與原生安全性如何平衡(POS 鏈視角)
BTC Staking 並不意味著要完全取代原生代幣的質押。實際上,PoS 的項目方可以有兩種(比特幣 + 原生代幣)甚至更多元的質押資產組合來保障自身的安全性。而考慮到用戶持有比特幣和原生代幣的持有成本不同,兩者的質押獎勵往往也需要額外設計。質押獎勵的形式可能是原生代幣、收入分成等。
關於安全性,讓我們從資金的“分散程度”與“總量”這兩個維度去思考。
從資金的分散程度的角度來看是比較直覺的:在原有的質押資產與節點的基礎上,若是引入外部的質押資產與節點,無論是用哪種方式來結合,無疑可以增加其去中心化程度,為整體網絡增加韌性。具體的結合方式可以有:
- 原生的雙重質押:原生代幣運營商和 ETH 運營商被視為一個整體,不同運營商的質押份額通過外部價格進行轉換,有效共識只需要達到這個整體的門檻即可。
- 模塊化的雙重質押:有效共識需要原生代幣運營商和 ETH 運營商的支持人數各自均達到標準;這個達成共識的標準相對嚴格,同時也意味著,攻擊者可以僅攻擊安全性更低的運營商,就可以阻止共識的形成。
- 帶否決的雙重質押:原生代幣的運營商自行達到一定的數量標準,同傳統的 PoS 無異。ETH 運營商作為額外的一層保障,在原生代幣運營商犯錯時有權否決。該方案與模塊化的雙重質押在可用性上有差異:即使基於 ETH 的運營商均斷網,該方案下的 PoS 網絡也仍然能夠正常運轉。
從資金的總量上來看,我們可以從經濟安全的角度簡單算一筆賬,假設橋接到某條鏈上的資產 TVL 為 $5M,則為了達到 1.5 倍的安全閾值(對應 2/3 同意可以罰沒),質押資產的量級最好不低於 $7.5M。假設當前質押的原生代幣資產僅有 $5.5 M,意味著至少還有 $2M 的安全預算赤字。此時,可以優先考慮引入關係緊密的其他協議的代幣來作為輔助的質押資產,如果此時仍然有赤字,則可以考慮引入外部的安全性(BTC,ETH 等)。換句話說,Babylon 它們提供的服務如同僱傭軍,可以在不得已時通過付費獲取安全保障。
除了持有成本不同外,原生代幣的持有者在收到質押獎勵後更可能選擇繼續持有,而在質押的用戶收到獎勵後,鑒於他們本就是為了收益而來,他們極有可能很快拋售獎勵,為原生代幣帶來拋壓。從這個角度,項目方可以考慮以 Babylon 等提供的安全性作為補充,並權衡不同方案下的安全成本。這也意味著,項目方完全將安全外包出去是有風險的,擁有自己獨立的驗證者集及基於此的原生安全性仍然是一個更好的選擇。
綜合以上探討,從安全性租借方的角度來看,縱使租借比特幣或是以太坊的成本通常較低,但由於此資金的忠誠度不在自己的生態內,需要同時考量拋壓的隱患。另一方面,不同項目方對於資金總量與分散程度可以有不同的優先級,從經驗法則來看,向少數集中的資金提供者租借,通常單位成本會更低,但會以中心化為代價;不過這裡的核心在於,讓不同的項目方有選擇的權利。
如何選擇優良的安全性租借者(Node Operator 視角)
在一個完善的、去中心化的安全租賃雙邊市場當中,資金的提供者(即安全性的提供者)應該能自由地選擇要質押到任一特定 AVS 上。但假使 AVS 生態如預期大繁榮,在數百個 AVS 中該如何做正確的選擇與分配?我們認為,優良的定義應該是回報與安全性的平衡。
不論是個人質押(Solo Staking),或是將資金提供給 Staking Provider ,其選擇邏輯本質與傳統節點運營商(Node Operators, NOs)相同,可以直接借鑒他們所累積下來的經驗。通用的篩選標準例如確保租借方有良好的開發團隊與好的公開可檢視的代碼、產品的理念以及收益的永續性、給到安全性提供者的獎勵比例、團隊的過去經驗、項目的募資情況與投資者的信譽等等。
這裡的另一核心在於 AVS 最後的表現極可能會呈現冪律分佈(Power-Law Distribution),即回報集中在頭部的 AVS。所以能在早期介入優質的 AVS 會是 Alpha 的重要來源。這也意味著介入所有的長尾 AVS 不會是最優解,相反,它會帶來許多額外的複雜性和風險。Node Operator 可能需要因此收取高額的佣金費,從而降低質押用戶風險調整後的收益。同時,它也可能會引入更多的罰沒風險。
再往前思考一層,如果一個 AVS 公認有潛力,那麼大家對其代幣價值給予更多厚望,它就可以以相對較少數量的代幣獎勵租借到安全性。鑒於代幣價格是波動的,所以 Node Operator 也需要做好平衡,至少需要選擇部分以收入分成進行獎勵的 AVS,使其收益有下限保障。
安全性租賃市場後續會如何演進(Marketplace 視角)
區塊鏈世界的核心在於通過一套機制,讓各自自私的個體間,能以去信任的方式達成共識。在 PoS 的世界中,我們可以將共識理解為質押,而質押的可被罰沒性質又能被理解為安全性的來源,則“安全性租賃”也能理解成是一個將共識問題抽象化的手段,也就是區塊鏈世界的核心問題。
Babylon 它們在構建的服務可以類比為一個安全性的 Marketplace,其本質在於希望建立一個對“安全性”供給與需求進行撮合的雙邊效率市場。這裡的供給端指質押者,需求側則是有安全性租賃需求的 AVS。顯而易見的是,當前的困境在缺乏一個完整多樣的租借生態,能產生收益的 AVS 尚不多。破局之處在哪?從經濟學基本原理我們可以知道,短期看需求,長期看供給。
从需求側:
- 關於「是否有需求」,先不論需求的強烈程度,在我們最前面的論證可以理解到需求是真實存在的。後續如果 App Chain 的價值及市場定位可以被更廣泛的理解,或是有新型態的 AVS 能被設計問世,就能使安全性租賃的市場更加的穩健與繁榮。
- 關於「需求者是否能提供永續的真實收益」,我們認為在某種程度上是肯定的。例如 DA 層可以通過存儲收費、Oracle 可以通過提供數據收費、PoS 可以分享生態內的 MEV 收入與手續費等收益,這些收益都是真實且永續的。
從供給側,Babylon 需要說服比特幣社群其可以保障資產的安全性,Eigenlayer 則需要說服以太坊社群它們沒有過度使用以太坊的共識。從資金的穩定性角度,目前的質押資金可以隨時取回,此處興許可以考慮對於願意長期質押的資金提供更高的獎勵。此外,想建立優質的供給端,務實的手法是先讓「安全即服務」的概念可實踐,再使其易用,最後再做大做強。例如 Sreeram Kannan 講的故事就是將 Eigenlayer 打造成加密貨幣的雲端服務:通過規模效應,安全性提供方可以有效攤薄安全性的成本,也讓安全性使用方隨著業務的發展,擁有可即時擴展性的能力。另外,建立於 Eigenlayer 之上的 AVS 們,也能走模組化服務的路線,為其他的項目與生態,提供類似提供 SaaS 的體驗,這樣就能圍繞著安全性提供商 Eigenlayer 與 AVS 之間,建立一個強大且有韌性的生態。
搭載 Restaking 的 N 種方式
作為今年乃至未來一段時間內的重要敘事和行業基礎設施的完善,不同的項目方難免需要思考如何將自己的業務與 Restaking 有機的結合起來。我們認為,粗略可以分為兩個大的方向:
方向一:整合 Restaking 相關的資產
對於 DeFi 相關的應用,其通常可以直觀考慮如何將 Restaking 類資產整合到自己的業務場景中,潛在的一些方向比如基於質押資產做抵押借貸,提供流動性等,從而增加質押資產的效用。
以 Bedrock 為例,作為一個專門的流動性再質押協議,其新推出了 uniBTC,為以太坊上的 wBTC 持有者提供了一個實現 Restaking 的方案。相比直接在 Babylon 上質押,持有 uniBTC 流動性更強,且除了獲得 Babylon 本身的收益獎勵外,還可以獲得 Bedrock 的鑽石積分獎勵,從而提升整體收益。
此外,也可以參照收益平台 Solv Protocl,其將 Babylon 的再質押收益整合到了其 delta 中性的收益策略中。
 |
|---|
| Source: https://solvprotocol.medium.com/solvbtc-will-integrate-restaking-yield-from-babylon-1dba0c5a5193 |
方向二:作為 Infra 租用安全性
租用安全性則是一個更普世的應用場景。對去中心化有較高的要求而初始質押資本較少的 Infra 皆可以考慮租用。一些潛在的 AVS 方向比如:Rollup 相關的服務(排序器、橋、MEV 相關的服務等),協處理器(可驗證的數據庫,AI 界面等,代表案例:Ritual),一些加密應用(TEE Network,秘密共享,FHE 等,代表案例:Inco、Fhenix),一些證明應用(身份、地址證明等)等。這裡面有一些 AVS 開拓了此前從未有過的鏈上新場景,尤其是協處理器這塊可以有很多創新,加密應用這塊也才剛起步。
以新近宣布做 L2 的 Cyber 為例,其基於 Eigenlayer 的 AVS 搭建包括排序器、驗證者、CyberDB 在內的去中心化 Infra。雖然其合作的是 Eigenlayer 而非 Babylon,但就租用安全性層面來說,兩者實質相同。Cyber 採用了雙重質押模型,用戶可以質押 Cyber 或 LRT 資產(目前支持 ezETH、pufETH、weETH)獲取多重收益,包括 ETH 的質押收益,Eigenlayer 的再質押收益和積分、LRT 積分、Cyber 再質押積分等,相當於 AVS 的安全性同時用 Cyber+ LRT token 來保證。

雙重質押模式有個優點:可以通過租用 ETH 助力網絡冷啟動,並減輕死亡螺旋的影響。比如當原生代幣價格下跌時,PoS 網絡的安全雖然會受到影響,但後果相對可控,畢竟有 LRT 資產提供的經濟安全保障打底。
結語
安全是區塊鏈的核心命脈,把加密貨幣市值最大的兩種代幣的安全性開放給其他應用與開發者無疑會產生持久而深遠的影響。Restaking 也因此當之無愧是區塊鏈世界演進的主航道上的敘事。在這個過程中,我們看到行業內頂級的創業者在直面關鍵問題,利用最新的技術可行性,不斷向前探索最優解,突破比特幣與以太坊原有的限制。
如果限定地來看 PoW 與 PoS 世界之間的安全性的共享,使用第一性的原則可以將其分為 [PoW, PoS] x [PoW, PoS] 四種類型:
- PoW → PoW :常見的手段是合併挖礦(Merged Mining),比如 Rootstock。
- PoS → PoS:比如「Eigenlayer 的再質押」與「Cosmos 生態系上的 Hub 與 Zone」皆屬於此。
- PoW → PoS:比如 Babylon 將 PoW 的資產作為 PoS 的質押資產。
- PoS → PoW:這一塊是比較少被探索的,但一種直觀的想法可以是,兩者間可以通過 RWA 資產的轉換,將代幣化後的算力用於 PoW 之上。
如果更廣義地來看安全性租賃,其關鍵在於底層的共識如何達成,如何把這種共識協議化、產品化、規模化,並在此基礎上建立一個繁榮的雲端服務生態。各項 AVS 服務並非是孤島,互相之間高效的協同,更好的資源利用和數據共享,才更符合 Cypherpunk 初始的精神,也是真正價值的來源。
這裡面還有許多的可能性未曾展開,比如 AVS 收益的合理分配範式、新型 AVS 的湧現、各項服務的樂高組合等。我們認為,關於 Restaking 的探索才剛剛開始,值得持續關注這個方向的演進、迭代與伴隨而生的機會。